Reading in between the lines
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to
Date
Transaction
Account
Amount
Payment Mode
Originates from
Destined to

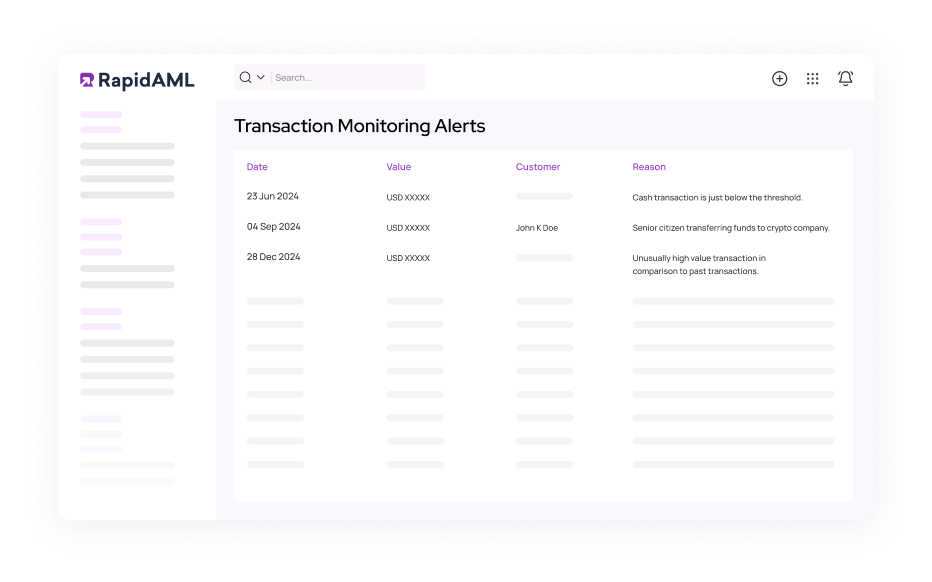
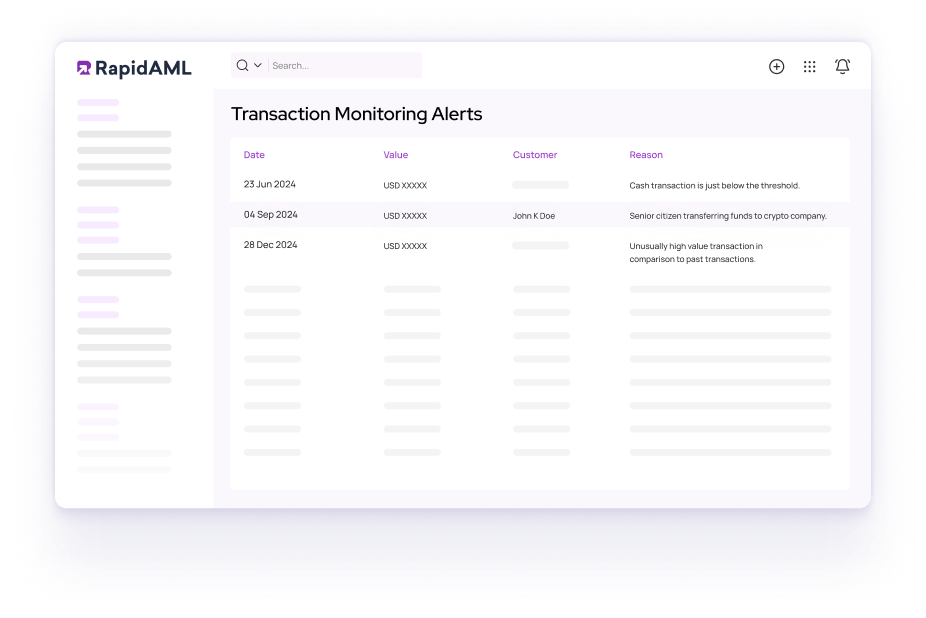
Detect Suspicious Transactions in Real-Time with Our Transaction Monitoring Software
Cue dramatic orchestral music.
Tonight, dear reader, we enter a place where wealth flows like a river through gilded gates. Steady, glittering, and sometimes carrying secrets beneath its shimmering surface, deceptions move as gracefully as a well-rehearsed dance. Transaction monitoring is an unseen sentinel. It doesn’t sleep. It doesn’t blink. And certainly, doesn’t fall for smooth talk.
Cut to: A shadowed figure watching from the balcony.
The rules are set, the red flags raised, and with a whisper in the right ear, the music slows. Close-up to our watchful guardian. A sophisticated AI-driven system, faster than a hawk spotting its prey. Powered by next-gen technology, it moves swiftly, setting off alerts and tracing each suspicious step.
Roll credits. Fade to black.
The Watchlist
Silent movements, loud consequences
Season 1
When money starts moving in strange ways, trouble is often afoot. A faint irregularity in the flow of transactions is barely noticeable to the untrained eye. But RapidAML is no ordinary observer. It watches. It learns. It remembers. And when something doesn’t add up, it doesn’t look away. A routine transfer, but the numbers don’t sit right. A dormant account suddenly springs to life. A pattern that feels deliberate. The alert is triggered. Is it a coincidence? A false alarm or the first crack in a carefully constructed façade? As Shakespeare warned, “Suspicion always haunts the guilty mind.” But is there guilt? One thing is certain this is no coincidence in compliance. The investigation begins.
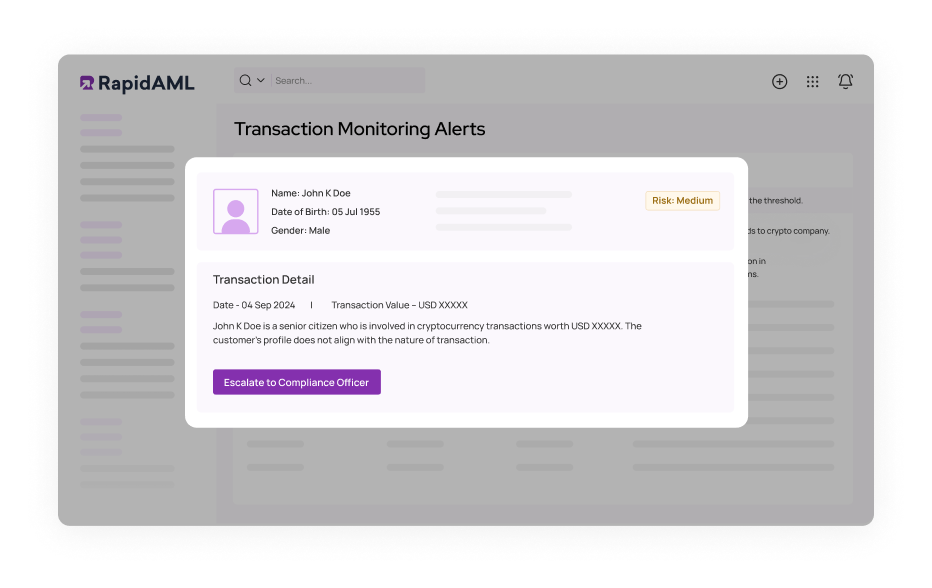
Season 2
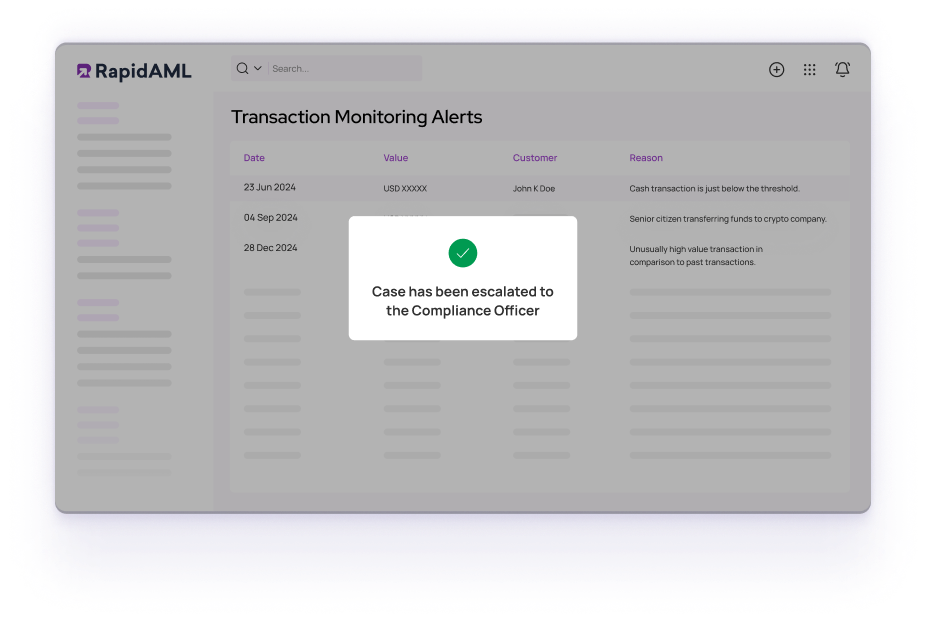
An alert isn’t noise, it’s a signal. So, the case is opened. The fleeting anomaly is now a full-blown investigation. A footprint in the snow. Subtle, yet undeniable. Case creation is at the core of the process, systematically linking every alert, transaction, and risk indicator into a single, cohesive file. Now that the case has a name, a structure, and a trail to follow, the real story begins.
But something still doesn’t sit right. The more data pours in, the more it feels like this isn’t a one-off event. The details are lining up too neatly, the anomalies too well-placed. This isn’t just a case. It’s the first thread in a much bigger web. And pulling it? Well, that’s a story for another story.
Season 3
Like any good story, the team gathers intel. This isn’t just data, it’s a trail left behind by those who think they can outsmart the system. The Internal Files hold the truth, but only for those who dare to look close enough. Reports stack up as unsolved case files and transaction patterns emerge like shadows shifting in the dim glow of a midnight streetlamp.
An unusual transaction pattern, a connection that shouldn’t exist, they are the breadcrumbs that separate coincidence from conspiracy. The case is no longer a hunch. RapidAML moves methodically, compiling internal reports with every transaction linked and every clue preserved. Risk assessments are run, transaction histories dissected, and behaviours scrutinised. Is this a lone wolf or part of a bigger pack? The team is watching, waiting. The moment you think you’re safe is the moment you’ve already been caught.
Season 4
Not all secrets are hidden in dusty filing cabinets or encrypted databases. Sometimes, the truth prefers the great outdoors in external reports, regulatory filings, or warnings from financial keepers. In this season, the case goes global, and one wrong step could turn a routine check into an international thriller. It takes a village to raise a child, but it takes an entire network of compliance officers, regulators, and financial institutions to catch money launderers. Each report and red flag is another flashlight beam cutting through the dark, exposing the spectres of corruption and crime. The hunt extends across jurisdictions because where there’s smoke, there’s usually someone trying to launder fire.
Is this a one-time fluke or part of a larger pattern? Industry-specific red flags are cross-checked, past behaviours are analysed, and monitoring rules are configured to match the organisation’s risk appetite and AML framework. What might seem harmless in one industry could scream money laundering in another.
Some institutions build towering walls, blocking every risk in sight. Others prefer hidden traps, subtle enough to catch only the truly cunning. But the most powerful? They design. No two businesses face the same threat. What you need is a system that bends, adapts, and moves in sync with your risk appetite. Decide how the game is played with customisable monitoring rules. Set the thresholds, tweak the parameters and let the system align with your AML framework and not the other way around. Want a sharp, high-alert strategy that catches even the faintest suspicious? Done. Prefer a refined risk-based approach that filters and focuses on the real dangers? Consider it done.
Ever had your email wrongly flagged that super important message as spam while letting an obvious scam about a long-lost prince’s inheritance get right through? Now imagine that happening in compliance, where false alerts flood your team while real threats slip under the radar. Our adaptive machine learning works like a VIP security guard with a photographic memory who knows exactly who to let in, who needs a second look, and who’s absolutely suspicious. It learns from past cases, refining risk detection every single time so your team isn’t stuck investigating harmless transactions. Like a GPS that reroutes based on live traffic updates, our traffic adjusts in real time.
The regulator’s letter arrived at dawn. Cryptic, urgent and unforgiving. The audit clock has started ticking, and one wrong move could turn compliance from a formality into a full-scale investigation. A quiet hum filled the air. Our system has already spoken. Transactions? Logged. Alerts? Traced. Investigations? Tied up in neat, undeniable records. No gaps. No mysteries. A trail leading exactly where it should. To the truth. A system that anticipates the unknown, reporting isn’t a race against time. It’s a script already written, waiting for the final signature.
All Illusions are Real Until They’re Questioned
Coincidence is the Comfort of the Incurious
Money moves like whispers in the wind. Soft, silent, invisible, and sometimes deeply deceptive. Arthur, once a poet before numbers consumed him, saw a story where others saw figures. Where they saw ledgers and line items, he saw stories waiting to betray their authors. There, in the constellations of data, was a crime not yet confessed. As Arthur leaned forward, fingers poised over his keyboard, a voice murmured, “Look again,”. He froze. The voice wasn’t external. It was his own voice, or at least some version of it, mocking him from the depth of his mind. He realised this was no longer just a job. It was a hunt.
| Alerts, Alerts Everywhere | Relax, We’ve Got This |
|---|---|
|
Arthur’s Conscious:Friends, Romans, countrymen, lend me your ears! Look at them. A thousand alarms, each more than the last. A florist wiring money to a tulip farm? SUSPICIOUS! A lawyer moving client funds? TREACHERY! Congratulations, you’ve become a detective for the mundane.
Arthur: This transaction monitoring system is a circus. |
Not every ripple in the water signals a shark. Let the machine think before you panic. Wasting time on transactions as harmless as a grandmother sending money to her cat’s inheritance funds is like chasing phantoms. No more. RapidAML’s adaptive machine learning will silence the noise, separating the true threats from the innocent. From now on, every alert is a call to arms, not a fool’s errand. |
|
Arthur’s Conscious: Tell me, Arthur. Where is the evidence? In your inbox? An excel? That yellow notepad buried under your teacup? Oh, what a spider's web we weave. Arthur: My sanity is eroding like sand slipping through an hourglass. |
Every case is a tangled mess demanding the patience of a saint. You can have a structured case file instead of a chaotic mess. Not just a file. A weapon. RapidAML brings systematic case creation, where alerts are neatly documented and arranged like a detective’s notebook in perfect order. |
|
Arthur’s Conscious: Ah, the quarterly report. Tick-tock, Arthur. That report is due in two hours, and your current ‘system’ is a mix of hope, prayer, and CTRL+V. Will the regulators spare you this time? Who knows?
Arthur: I’d be up at midnight, frantically piecing together compliance reports like some tragic Shakespearean fool? |
The shadows feast on the chaos and love watching men crumbling under the weight of deadlines. Be the playwright with RapidAML, not the tragic hero. A report so flawlessly crafted it might as well walk into the regulator’s office, tip its hat, and hand itself over with a flourish. It doesn’t beg for extensions. It doesn’t break under pressure. It doesn’t mysteriously disappear the moment you need it most. |
|
Arthur’s Conscious: Look at them, Arthur. The clever ones. Breaking transactions into smaller amounts. Shuffling funds like street magicians. And you? You are the audience, always a step behind.
Arthur: A real estate laundering scheme looks like a normal business, while, trade-based money laundering sails through unnoticed. |
Arthur, you shall no longer be blind. This is textbook structuring, and RapidAML will spot it instantly. The game is over before it even begins. Financial criminals don’t announce their intentions. They bury them under layers of transactions. |
|
Arthur’s Conscious: Too late, Arthur. The money’s already moved. The accounts are closed. The trail is cold. You always arrive after the crime, never before.
Arthur: How can I stop crime while it’s happening? Static rules become obsolete, new laundering techniques slip past unnoticed. |
The best defence is not preparation but evolution. Financial crime is not static. It morphs, adapts, and reinvents itself. A system that cannot evolve is doomed to fail. RapidAML detects advanced risk continuously and refines itself, learning from patterns and anticipating new threats. |
The dark age of transactions has ended. At some point, we all face a choice. Keep struggling with outdated systems or finally step into a world where things just work. You can keep scrambling at the eleventh hour, whispering promises to “be more organized next time.” Or, you can let go of the madness. Real efficiency is about walking into an audit with confidence instead of caffeine-fueled anxiety. Do you want to keep struggling, or do you finally want peace of mind?
Seeing Beyond the Numbers
In compliance, as in life, the unseen is often more dangerous than the obvious. RapidAML doesn’t just track movements, it uncovers intent, piecing together the puzzle.
The chase begins here. Are you in? Book a demo and step into a world where risk is anticipated. In the end, what you don’t question may already control you.
The Art of Seeing
Not all deceptions are loud. Some hide in plain sight, disguised as routine transactions, buried within everyday financial flows. The key to uncovering it? Knowing where to look. Our exclusive eBook takes you beyond surface-level compliance, revealing hidden patterns, red flags, and cues that turn suspicion into certainty.
Solutions
Services
Industries
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
© RapidAML 2025
Solutions
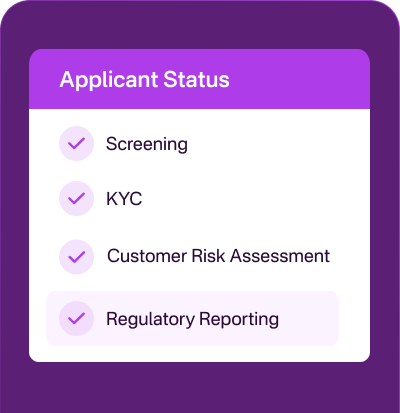
Screening
KYC
Customer Risk Assessment
Case Management
Transaction Monitoring
Regulatory Reporting
Services
Enterprise-Wide Risk Assessment
AML/CFT Health Check
Industries
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
Lorem Ipsum
© RapidAML 2025
Get Started
Contact Us